Exploitation¶
In this section I’ll explain you how to exploit the found vulnerabilities.
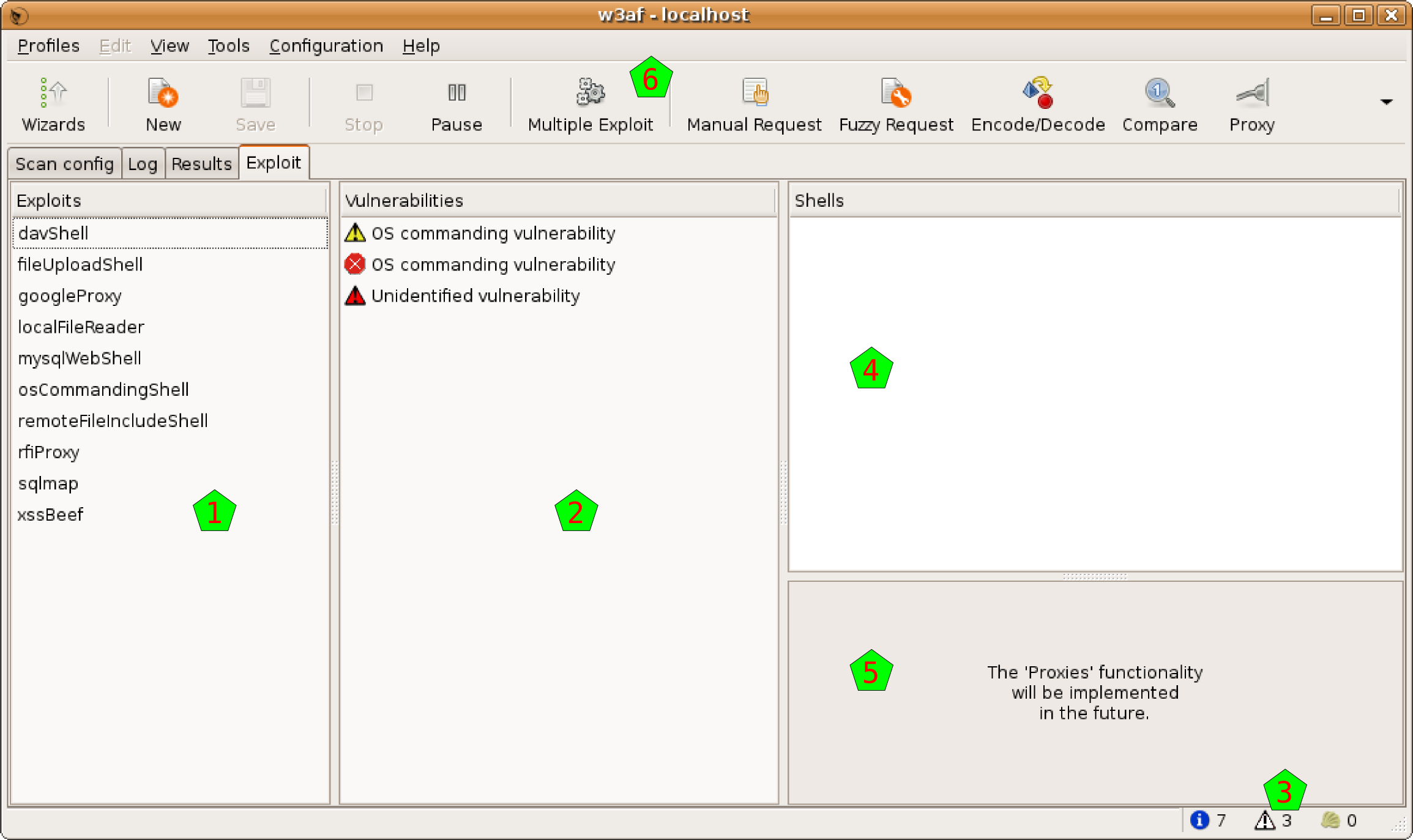
When the scan is running or after the scan finished running, as you can check the results, you also can start with the exploitation. For this, go to the fourth tab in the system, called Exploit:
This window is separated in different panes. At the very left [1] you have a list of all the exploits that you can execute over the vulnerabilities that you found, which are listed in the second column [2]. You can see there that we found three vulnerabilities, as you can also check in the left bottom corner of the window [3].
At the right part of the window, there’re two panes: one [4] for the exploited shells (more on this below), and one [5] for the proxies (this functionality is not yet developed).
Finally, you can see that when you enter to this tab, the Multiple Exploit button in the toolbar [6] is enabled.
Executing an exploit¶
Exploits act on vulnerabilities. But not all exploits act on every vulnerabilities. It is well known if any exploit could act on some vulnerability, though, but to be sure and actually exploit it some verification needs to be done. Fortunately, the system easies very much this process to you.
To exploit a vulnerability, you need to drag the exploit and drop it on the vulnerability you want to exploit. This drag & drop process is all you need to activate one specific exploit; if you want multiple exploiting see below. But, as all exploits don’t act on all vulnerabilities, how do you know what to drag and drop where?
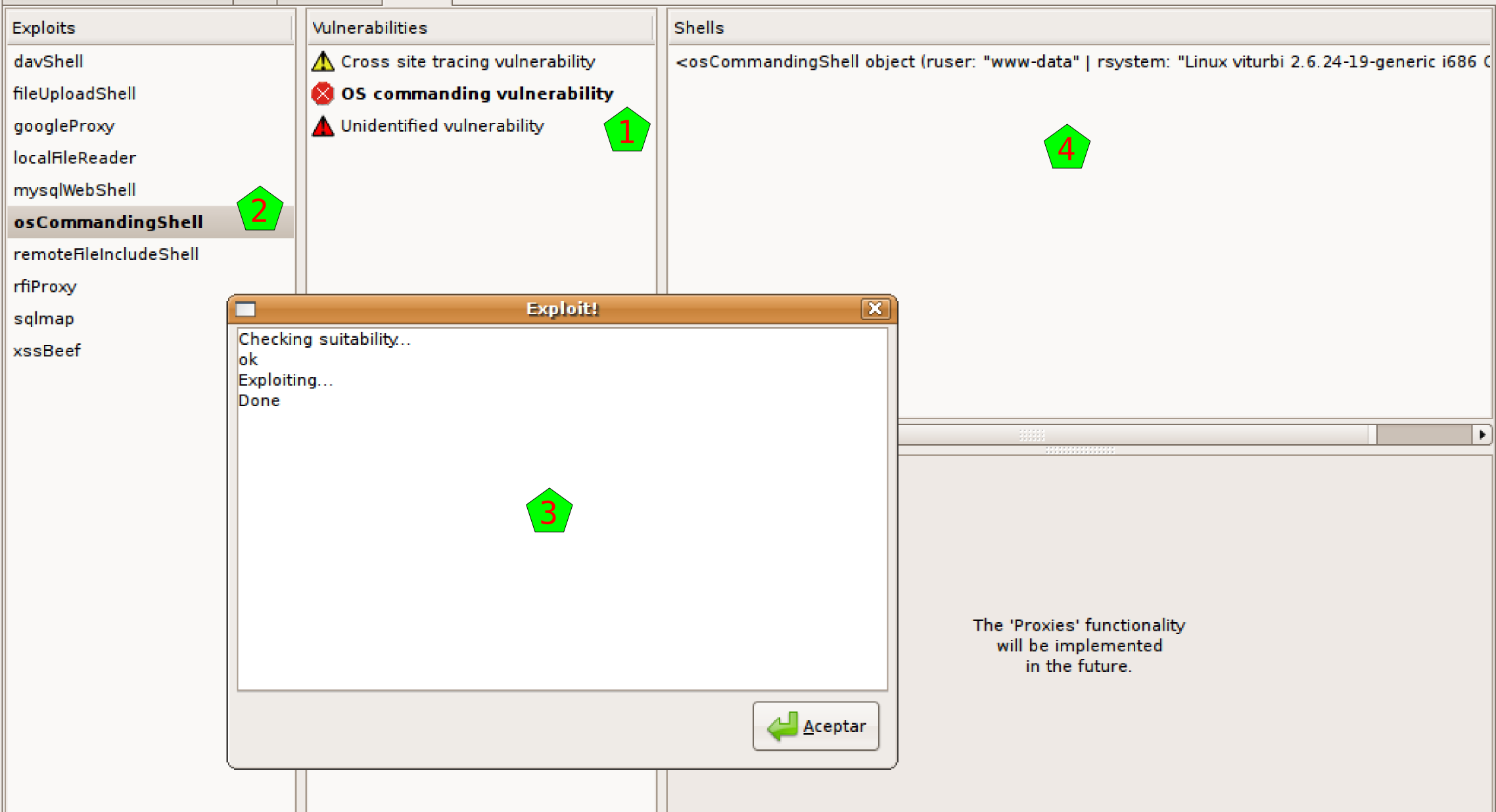
When you click on any exploit, the system will put in bold font those vulnerabilities that could be exploited by that exploit [1]. This works also in the other way: if you click on any vulnerability, the system will put in bold those exploits that could act on that vulnerability [2]. I put emphasis on the “could”, because there’s no certainty that the match will be useful… but for sure, if you trigger an exploit over a vulnerability that don’t have both fonts in bold, it will not act.
On the other hand, if you actually drag a marked exploit on a marked vulnerability, the system will try to exploit it. A new window will pop up [3], showing the actions that the system is taken. See in the example that the system first checks the suitability of that exploit over that vulnerability, and if OK, it actually triggers the exploit.
In the example, everything is fine and the exploit succeeds, creating a shell in the shell window [4].
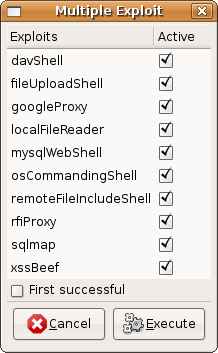
If you want to trigger more than one exploit at once, you should click on the Multiple Exploit button in the toolbar, and a window like the one here at the right will appear. There you can select all the exploits that you want to trigger, and when you click on the Execute button, the system will try all the marked exploits on all the possible vulnerabilities. If you activate the First successful checkbox, the system will stop after the first time that an exploit succeeds when working on any vulnerability.
Using a shell¶
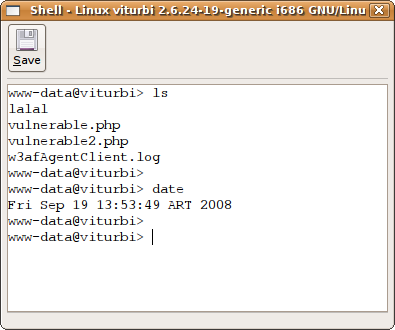
If the vulnerability generates a Shell as the result of being exploited, you will see the shell (or shells if it generates more than one) appear in a pane of this window, as we saw above.
If you double click on that shell, you will start using it, and a new window will pop up for you to use it, a window very similar to the one you see here at the right.
There you can see that you have a shell like environment. Well, it is exactly that: it is the shell opened in the remote equipment as a result of the exploited vulnerability.
Also, you have a Save button that let you save all the session to a file, in the case you want to keep all the text for a later analysis.